Attack Surface & Exposure Assessment
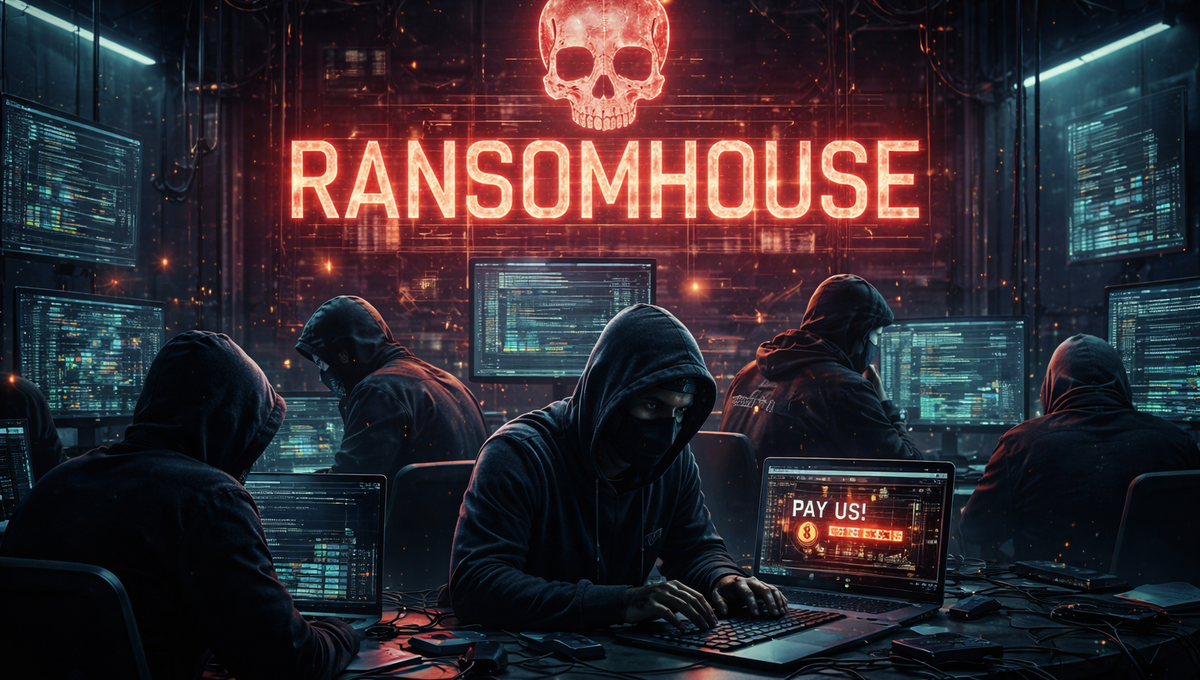
Threat & Attack Surface Assessment
Fortura’s Threat & Attack Surface Assessment uses open-source intelligence (OSINT) to identify externally observable exposure across systems, identities, and services, then assesses how real-world threats could exploit that exposure in the context of your business.