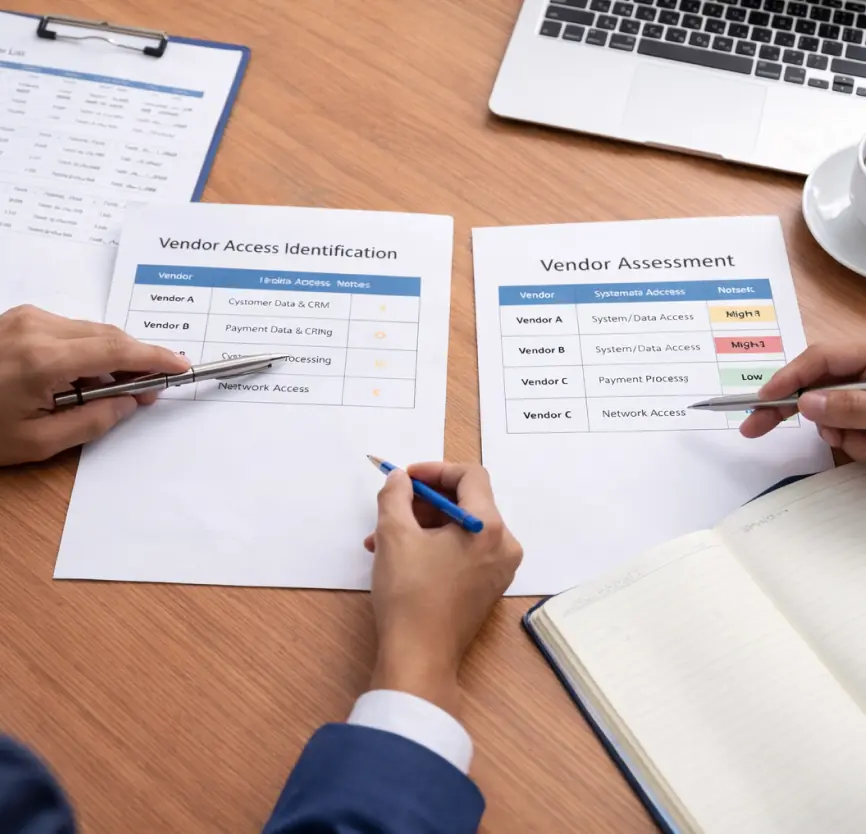
Third-Party Risk Assessment
Understand risk by your vendors and service providers
Fortura’s Third-Party Risk Assessment helps organizations evaluate cyber risk associated with external vendors and service providers, focusing on how third parties access, process, or support critical business systems and data.