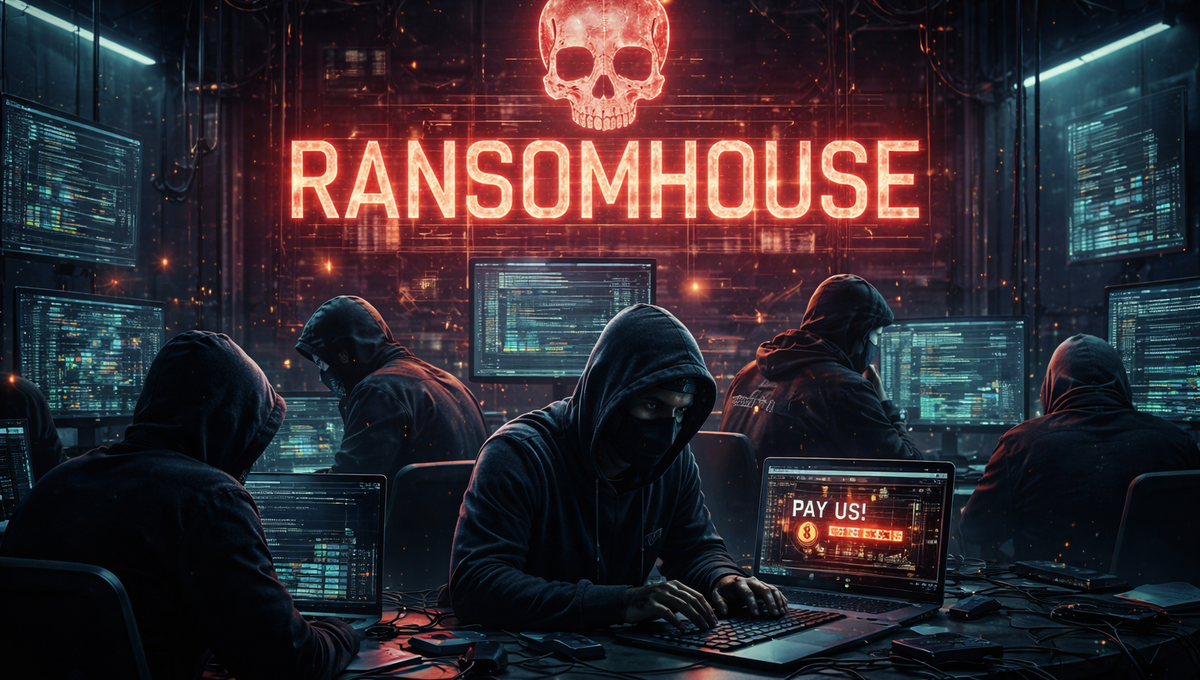
Security Program Design
Design a Security Program that Aligns to Risk, Not just Controls
Fortura’s Security Program Design service helps organizations structure their security strategy, governance, and operating model around real risk, business priorities, and threat reality — creating a program that is coherent, defensible, and executable.